
About

Headquartered in Columbus, Ohio, SRMC is a certified woman-owned, independent security consulting organization that brings real-world experience and expertise to their clients. We provide holistic, high-quality, and professional solutions for complex security challenges.
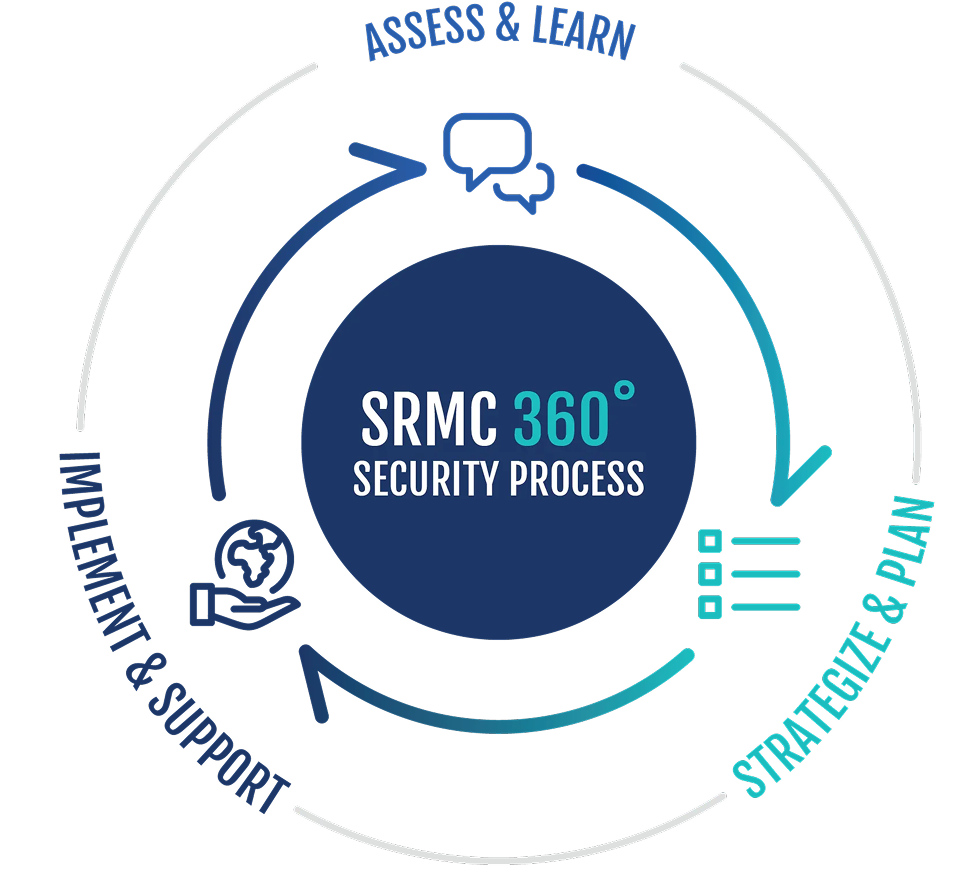
The SRMC 360º Security Process assesses each client's unique security situation (assets, risks, technologies, personnel, culture), creates custom solutions aligned with business needs and best practices, and supports implementation through programs, technology enhancements, and ongoing services to ensure comprehensive protection.
First, we start with a comprehensive review of your security situation. Every client is unique, so we take the time to learn about not only your current security program and technology needs, but also your vision and values.
Next, we apply our 35+ years of real-world expertise to all that we have learned about your organization to create a custom security solution that both aligns with your needs and upholds strong security standards.
After strategically planning, we stand with you. We will help you implement, test, train for, and manage your physical security operations and technology needs while providing ongoing consulting support.
We believe in always doing the right thing, even when it hurts.
We always act ethically and on our clients’ behalf. We adhere to the Code of Conduct and Ethics of the International Association of Professional Security Consultants (IAPSC) and ASIS
We believe in making quality personal.
We invest in our people, technology, and capital infrastructure. Staff training, including participation in local, regional and national programs, is a priority, and without proper tools we can’t provide quality, efficient services to our clients.
We view our clients as relationships, not transactions.
We recognize that no two clients are the same. It’s our mission to develop security solutions designed specifically to meet our clients’ cultural and organizational needs. We also respect the confidentiality of our client relationships, and always perform our work ethically and professionally.
We believe that every question is a good question.
Projects are discussed internally, and issues are addressed from a team perspective. We believe our team's knowledge and skills far exceed the sum of our individual experiences.
We know trust is built on openness and honesty.
We believe that clients who are educated regarding industry best practices in physical security technologies and operational processes make better decisions for their organizations. Because of that, we share our ideas and innovations to help them be more successful.
SRMC is actively engaged with key industry and professional associations such as:
A security consultant is considered independent when they have no affiliation with the sale or installation of security hardware or the provision of guard services, and when they neither pay nor receive finder’s fees, commissions, or other financial incentives related to security products or services.
A security consultant brings independence of thought to both process-driven recommendations and holistic security solutions, whereas an integrator is inherently limited to technology as the primary means of addressing security challenges. Because SRMC does not sell security technologies, we evaluate security from a comprehensive perspective of people, processes, and technology with our clients’ best interests as the sole driver.
We do not recommend unnecessary solutions or promote technology for profit; instead, our guidance is objective, needs-based, and aligned with what is truly required to achieve your security objectives.
Layered security is a comprehensive approach that uses overlapping strategies and solutions to create a robust and effective protection plan tailored to your needs. These layers may include physical controls, security technology, policies and procedures, and security staffing, as appropriate. Layered security can be visualized as concentric circles of protection extending from the perimeter of the property, to the building exterior, and into interior spaces. By establishing multiple, integrated layers between the outside environment and the assets being protected, organizations significantly enhance their ability to deter, detect, and respond to threats.
Employees provide a valuable and often distinct perspective on the effectiveness of current security measures one that may differ from the viewpoints of administrators or consultants. Recognizing that large-scale change can be challenging, involving employees in discussions about their perceptions of safety and security helps them feel engaged and invested in the solution. This inclusive approach facilitates smoother implementation of process improvements, technology enhancements, security awareness training, and other critical components of a successful security program.
A common concern among higher education clients is whether their institution is in compliance with the Clery Act. While legal determinations should always be made in consultation with your General Counsel, as SRMC provides security consulting rather than legal advice, we can conduct a comprehensive review of your Annual Security Report and related policies and practices. Based on this review, SRMC offers informed, practical recommendations grounded in our extensive experience with Clery requirements.
SRMC consultants bring unparalleled subject matter expertise in this area. Our team includes professionals who have served as a Clery Coordinator at a major university for more than 20 years, participated on the U.S. Department of Education’s Negotiated Rulemaking Committee for VAWA/Clery, provided testimony before the U.S. Senate, and contributed to congressional hearings on these critical laws.
In addition, SRMC’s expertise extends well beyond Clery compliance. Our multidisciplinary team routinely evaluates policies, procedures, and practices against a wide range of professional standards, including accreditation requirements, training standards, emergency management frameworks, and best practices for entertainment and sporting events.
Security benchmarking is the process of comparing your organization’s key performance metrics with those of peer organizations within the same industry. The most effective benchmarking evaluates organizations with similar characteristics, such as operating environment, size, geographic location, number of employees, and customer or population demographics.
Public safety and security operations may also be evaluated against survey data and studies compiled by academic institutions, professional associations, or public sector sources.
As part of the SRMC assessment process, benchmark research can be conducted and incorporated as a comparative reference point at the client’s request, providing additional context to inform findings and recommendations.
SRMC differs from an engineering firm that designs security systems in both role and perspective. While engineering firms typically focus on the design and technical specification of security infrastructure, SRMC operates as an independent, vendor neutral security consulting firm whose sole responsibility is to represent the client’s interests.
First, SRMC begins with risk, not technology. Our work starts by understanding your mission, culture, operating environment, regulatory requirements, and risk profile. We evaluate threats, vulnerabilities, and operational practices before considering solutions. Engineering firms are often engaged after a solution has already been assumed and are primarily tasked with designing systems to support that solution.
Second, SRMC takes a holistic, people, process, technology approach. While engineering firms appropriately emphasize technical design, SRMC evaluates security as an integrated program that includes governance, policies, procedures, staffing, training, and culture alongside technology. This ensures that technology supports operations rather than becoming a stand alone or misaligned investment.
Third, SRMC is fully independent and vendor neutral. We do not sell, install, or maintain security systems, nor do we receive commissions or incentives from manufacturers or integrators. Our recommendations are based solely on what is necessary, defensible, and appropriate for your organization and not on a predefined system or preferred product set.
Fourth, SRMC provides strategic planning and prioritization. Beyond system design, we develop security master plans, phased implementation roadmaps, cost modeling, and prioritization strategies that align security investments with operational impact and budget realities. Engineering firms typically focus on project specific design deliverables rather than long-term security strategy.
Finally, SRMC serves as a trusted advisor and owner’s representative. We support clients through procurement, vendor evaluation, and implementation oversight to ensure systems meet operational needs and design intent. Our role is to advocate for you by bridging leadership, operations, IT, facilities, and vendors rather than to engineer a single solution.
In short, engineering firms design systems, while SRMC designs security programs ensuring that people, processes, and technology work together to reduce risk, improve safety, and deliver lasting value.
Confidentially and protection of both client and SRMC intellectual information is paramount as we understand the ramifications if data is compromised. SRMC deploys the most contemporary encryption and cyber security methods on network connections and servers as well as on staff issued laptops. We also invest in using a third-party, trusted, external cyber and network consultant to monitor our systems to ensure we are implementing the most secure measures available in the marketplace.
Yes, we do. We have been in business for 35+ years and over that span of time we have had the opportunity to work in nearly every market. It would be impossible to list all the types of organizations with whom we have done business but we pride ourselves on creating a unique relationship with each of our clients. If you do not see your business sector listed, just contact us to discuss your specific industry needs.
Security services and security consultants play distinct but complementary roles in protecting an organization. Security services focus on day-to-day operations, such as providing security officers, patrols, and incident response, while security consultants offer strategic, independent guidance to help organizations understand risk and determine the most effective security approach. Consultants evaluate people, processes, and technology, develop plans and recommendations, and help define requirements, while security services carry out and operate within those established frameworks.